A new malware variant called Popcorn Time poses victims with a tough choice: your files or your friends.
The ransomware, which is unrelated to the popular streaming website, is unique in allowing victims to spread the virus as a form of payment. The infected user also can pay 1 bitcoin, worth about $780, to recover files that have been encrypted.
The research group MalwareHunterTeam discovered the virus, which is still undergoing development. Here’s what you need to know about Popcorn Time malware.
1. You Have 7 Days To Infect Your Friends or Pay a Ransom if Infected
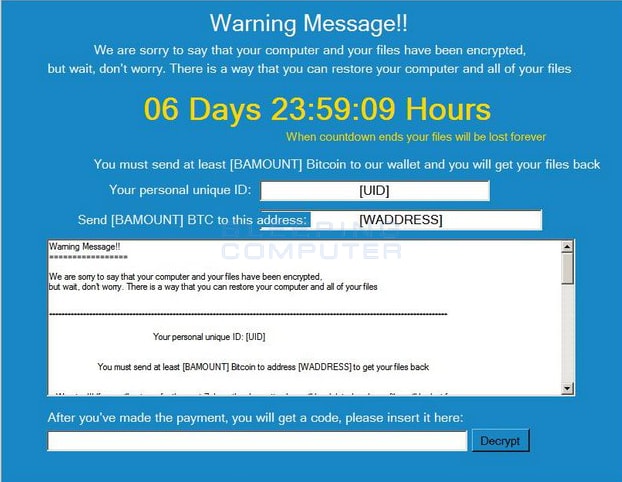
Popcorn Time malware gives victims seven days to pay a ransom before deleting his or her files. When the ransomware is downloaded, it will show a fake loading screen as it encrypts a user’s files making them inaccessible. Popcorn Time has been updated to encrypt files on a user’s My Desktop, My Pictures and My Music folders, according to cybersecurity site BleepingComputer.com.
Once the files are encrypted, a new screen showing a countdown and a ransom message will appear. Users can either pay 1 bitcoin to the provided Bitcoin address or infect two of their friends, and have them pay the fee instead. Once the user pays the ransom, they will get a decrypt code; you have four tries to type in the decrypt code before your files are deleted.
2. It’s Named After the BitTorrent Client Popcorn Time, which was Shut Down and then Revived
The malware ripped off the name of torrenting site Popcorn Time. The original Popcorn Time was shut down after a copyright infringement suit brought by the Motion Pictures Association of America followed by a series of DNS attacks. Since then, however, Popcorn Time variants have appeared under multiple domain names.
The code for the streaming site is also available on the coding platform Github. A new web version called Popcorn Time Online has since launched, which allows you to stream Torrents directly from the browser instead of having to download an app.
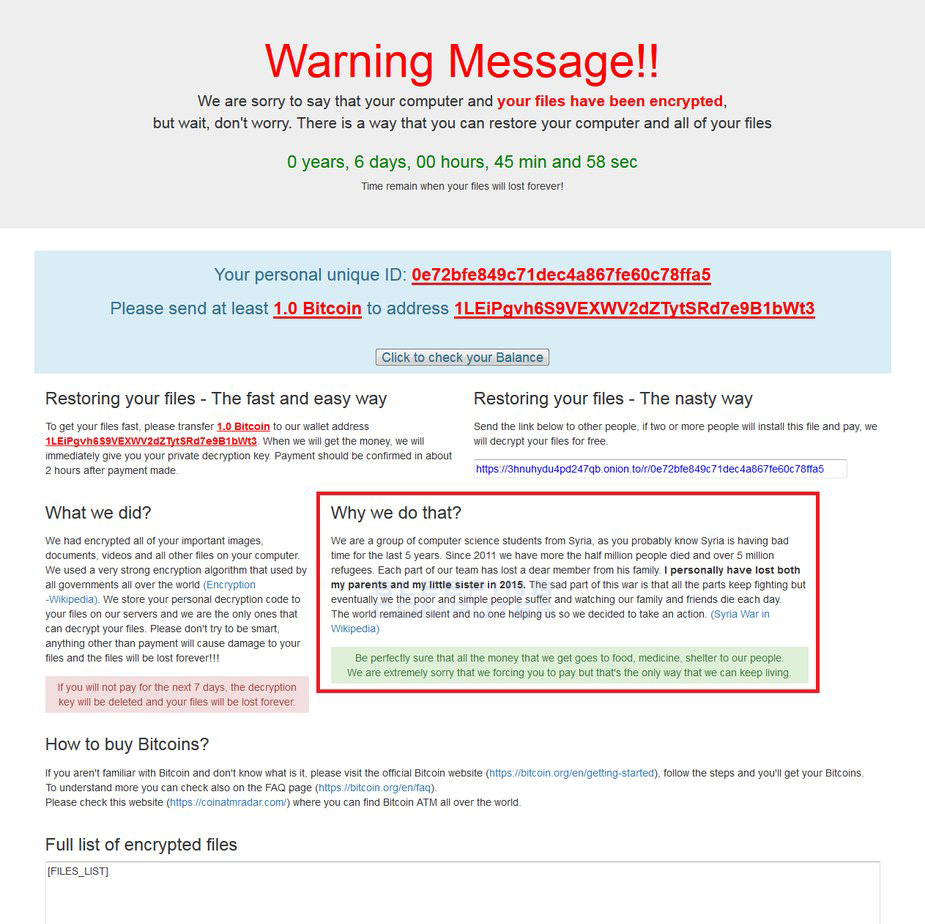
3. The Malware’s Creators Claim to be Computer Science Students from War-Torn Syria
The ransom screen that appears on Popcorn Time includes some backstory on the creators. They purport to be a group of computer science students from war-torn Syria, in desperate need of cash. The message says the money will go towards supplies for the affected families.
“Be perfectly sure that the money we get goes toward food, medicine and shelter to our people. We are extremely sorry we are forcing you to pay but that’s the only way we can go on living.”
4. Popcorn Time Malware is Undergoing Development and May or May Not Roll Out
On December 9, the owner of BleepingComputer.com reported that the malware’s code was updated with additional encryption location. Noticeably absent from the malware is the code for deleting files. However, Lawrence Abrams noted it wouldn’t be surprising if the code were added.
“It is still not perfect, but it’s getting better,” MalwareHunter told WIRED. “Infect more to get free key is already unique thing. This system is something you not see every day.”
5. You Can Take Precautions by Backing Up Your Files and Avoiding Suspicious Downloads
There are several precautions you can take to prevent losing your files. To avoid losing your files forever, you can backup your files on an external hard drive or cloud storage. Additionally, hackers exploit software vulnerabilities as well as natural curiosity of users. Be wary of phishing tactics, which spread when users click on malicious links within emails.
It’s unclear how Popcorn Time will trick users into installing it, Abrams reports. However, as a general rule of thumb, only download software from reputable sources. Download pages that appear over-the-top in advertising may be a warning sign that it contains dangerous software.